Share ECCouncil ECSAV10 exam practice questions and answers from leads4pass latest updated ECSAV10 dumps free of charge.
Get the latest uploaded ECSAV10 dumps pdf from google driver online. To get the full ECCouncil ECSAV10 dumps PDF or dumps
VCE visit: https://www.leads4pass.com/ecsav10.html (Q&As: 354). all ECCouncil ECSAV10 exam questions have been updated, the answer has been corrected!
Make sure your exam questions are real and effective to help you pass your first exam!
[ECCouncil ECSAV10 Dumps pdf] Latest ECCouncil ECSAV10 Dumps PDF collected by leads4pass Google Drive:
https://drive.google.com/file/d/1JI9OwDp9z1OAW86uUMeHs4vQyIeKYUck/
[ECCouncil ECSAV10 Youtube] ECCouncil ECSAV10 exam questions and answers are shared free of charge from Youtube watching uploads from leads4pass
Latest Update ECCouncil ECSAV10 Exam Practice Questions and Answers Online Test
QUESTION 1
The SnortMain () function begins by associating a set of handlers for the signals, Snort receives. It does this using the
signal () function. Which one of the following functions is used as a programspecific signal and the handler for this calls
the DropStats() function to output the current Snort statistics?
A. SIGUSR1
B. SIGTERM
C. SIGINT
D. SIGHUP
Correct Answer: A
QUESTION 2
Which of the following policies helps secure data and protects the privacy of organizational information?
A. Special-Access Policy
B. Document retention Policy
C. Cryptography Policy
D. Personal Security Policy
Correct Answer: C
QUESTION 3
Which one of the following is a command-line tool used for capturing data from the live network and copying those
packets to a file?
A. Wireshark: Capinfos
B. Wireshark: Tcpdump
C. Wireshark: Text2pcap
D. Wireshark: Dumpcap
Correct Answer: D
QUESTION 4
What is a good security method to prevent unauthorized users from “tailgating”?
A. Electronic key systems
B. Mantrap
C. Pick-resistant locks
D. Electronic combination locks
Correct Answer: B
QUESTION 5
Adam is working as a senior penetration tester at Eon Tech Services Ltd. The company asked him to perform
penetration testing on their database. The company informs Adam they use Microsoft SQL Server. As a part of the
penetration
testing, Adam wants to know the complete information about the company\\’s database. He uses the Nmap tool to get
the information.
Which of the following Nmap commands will Adam use to get the information?
A. nmap -p2051 –script ms-sql-info
B. nmap -p1801 –script ms-sql-info
C. nmap -p1443 –script ms-sql-info
D. nmap -p1521 –script ms-sql-info
Correct Answer: C
QUESTION 6
During the process of fingerprinting a web application environment, what do you need to do in order to analyze HTTP
and HTTPS request headers and the HTML source code?
A. Examine Source of the Available Pages
B. Perform Web Spidering
C. Perform Banner Grabbing
D. Check the HTTP and HTML Processing by the Browser
Correct Answer: D
QUESTION 7
In the TCP/IP model, the transport layer is responsible for the reliability and flow control from the source to the destination. TCP
provides the mechanism for flow control by allowing the sending and receiving hosts to communicate. A flow control
mechanism avoids the problem with a transmitting host overflowing the buffers in the receiving host.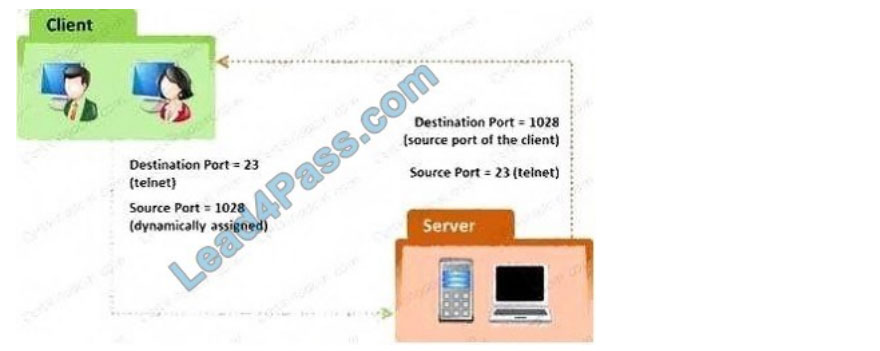
A. Sliding Windows
B. Windowing
C. Positive Acknowledgment with Retransmission (PAR)
D. Synchronization
Correct Answer: C
QUESTION 8
Which of the following password hashing algorithms is used in the NTLMv2 authentication mechanism?
A. AES
B. DES (ECB mode)
C. MD5
D. RC5
Correct Answer: C
QUESTION 9
Which one of the following is a supporting tool for 802.11 (wireless) packet injections, it spoofs 802.11 packets to verify
whether the access point is valid or not?
A. Airport
B. Aircrack
C. Airpwn
D. WEPCrack
Correct Answer: C
QUESTION 10
A penetration test consists of three phases: pre-attack phase, attack phase, and post-attack phase.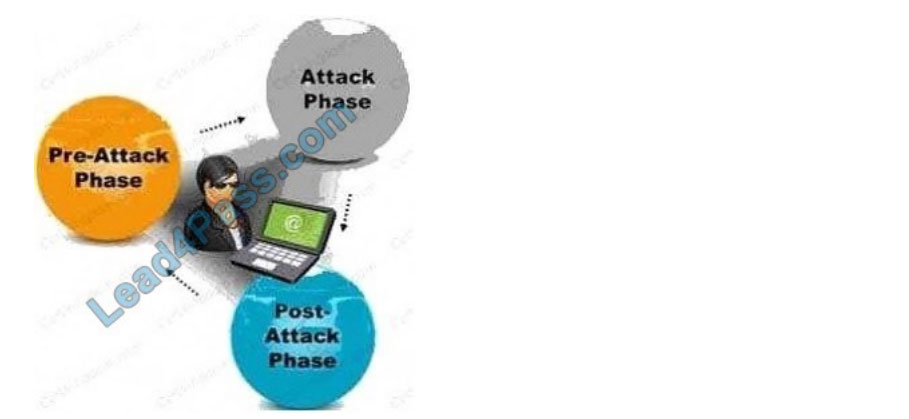
Active reconnaissance which includes activities such as network mapping, web profiling, and perimeter mapping is a part of which phase(s)?
A. Post-attack phase
B. Pre-attack phase and attack phase
C. Attack phase
D. pre-attack phase
Correct Answer: D
QUESTION 11
An attacker with a malicious intention decided to hack confidential data from the target organization. For acquiring such
information, he started testing IoT devices that are connected to the target network. He started monitoring the network
traffic passing between the IoT devices and the network to verify whether credentials are being transmitted in cleartext.
Further, he also tried to crack the passwords using well-known keywords across all the interfaces.
Which of the following IoT threats the attacker is trying to exploit?
A. Poor physical security
B. Poor authentication
C. Privacy concerns
D. Insecure firmware
Correct Answer: B
QUESTION 12
Which of the following statements is true about Multi-Layer Intrusion Detection Systems (mIDSs)?
A. Decreases consumed employee time and increases system uptime
B. Increases detection and reaction time
C. Increases response time
D. Both Decreases consumed employee time and increases system uptime and Increases response time
Correct Answer: A
QUESTION 13
During the reconnaissance phase of a penetration test, you discovered that the client has deployed a firewall that only
checks the TCP header information. Which of the following techniques would you use to bypass the firewall?
A. Bypassing the firewall using tiny fragments
B. Bypassing the firewall by manipulating the IPID sequence number
C. Bypassing the firewall source routing
D. Bypassing the firewall using the IP address in place of an URL
Correct Answer: A
For the full ECCouncil ECSAV10 exam dumps from leads4pass ECSAV10 Dumps pdf or Dumps VCE visit: https://www.leads4pass.com/ecsav10.html (Q&As: 354 dumps)
ps.
Get free ECCouncil ECSAV10 dumps PDF online: https://drive.google.com/file/d/1JI9OwDp9z1OAW86uUMeHs4vQyIeKYUck/